Introduction: The Expanding Importance of IT Support in a Digital-First World
Technology is no longer a supporting function in modern organizations—it is the foundation upon which operations, communication, customer experience, and revenue depend. In this environment, IT Support has evolved from a reactive troubleshooting service into a strategic safeguard that protects data, ensures compliance, builds trust, and reduces risk exposure. Whether a business operates locally or globally, the ability to maintain secure and reliable digital systems directly influences its stability and reputation. As cyber threats grow more sophisticated and regulatory requirements become stricter, IT support stands at the center of safety, trust, and risk protection.
This comprehensive guide examines how IT support safeguards organizations against cyber risks, enhances digital infrastructure, ensures compliance, and fosters long-term operational resilience.
Understanding the Core Functions of IT Support
At its foundation, IT support encompasses the maintenance, monitoring, and protection of hardware, software, networks, and cloud systems. However, modern IT support is layered and strategic. It includes:
- Helpdesk and end-user support
- Network monitoring and infrastructure management
- Cybersecurity implementation
- Data backup and disaster recovery
- Compliance management
- Cloud integration and maintenance
Most organizations structure IT support into tiered systems. Level 1 addresses everyday user issues such as login errors or software malfunctions. Level 2 resolves more complex technical problems, including system configuration and server management. Level 3 specialists handle cybersecurity architecture, system engineering, and high-level infrastructure planning.
Today’s IT support environment must align with established security frameworks such as those provided by the National Institute of Standards and Technology, which offers guidelines for identifying, protecting, detecting, responding to, and recovering from cybersecurity threats.
Cybersecurity Protection: IT Support as the First Line of Defense
Cybercrime has become one of the most significant global threats to businesses of all sizes. Ransomware attacks, phishing scams, data breaches, and insider threats can cause severe financial and reputational damage. IT support teams act as the primary defense mechanism against these dangers.
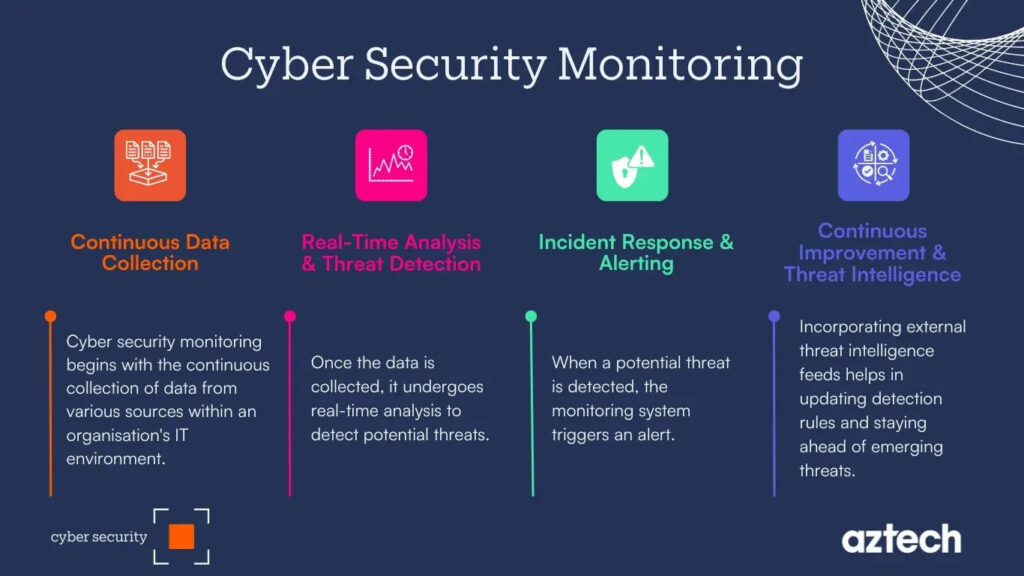
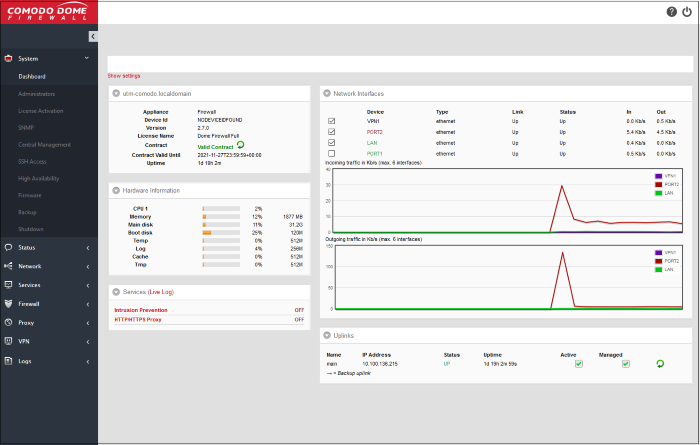
IT support professionals deploy firewalls, antivirus software, endpoint detection systems, intrusion prevention systems, and multi-factor authentication protocols. They also perform continuous monitoring through Security Operations Centers (SOCs), analyzing network activity to detect suspicious patterns before they escalate.
Patch management is another critical responsibility. Cybercriminals frequently exploit unpatched vulnerabilities. By ensuring that operating systems and software remain updated, IT support teams close potential entry points for attackers.
In addition, encryption and secure access controls protect sensitive data from unauthorized access. Whether customer information or proprietary company data, IT support ensures that confidentiality remains intact.
Risk Management and Business Continuity Planning
Risk management in the digital era requires careful planning and proactive mitigation strategies. IT support plays a key role in identifying vulnerabilities and implementing safeguards.

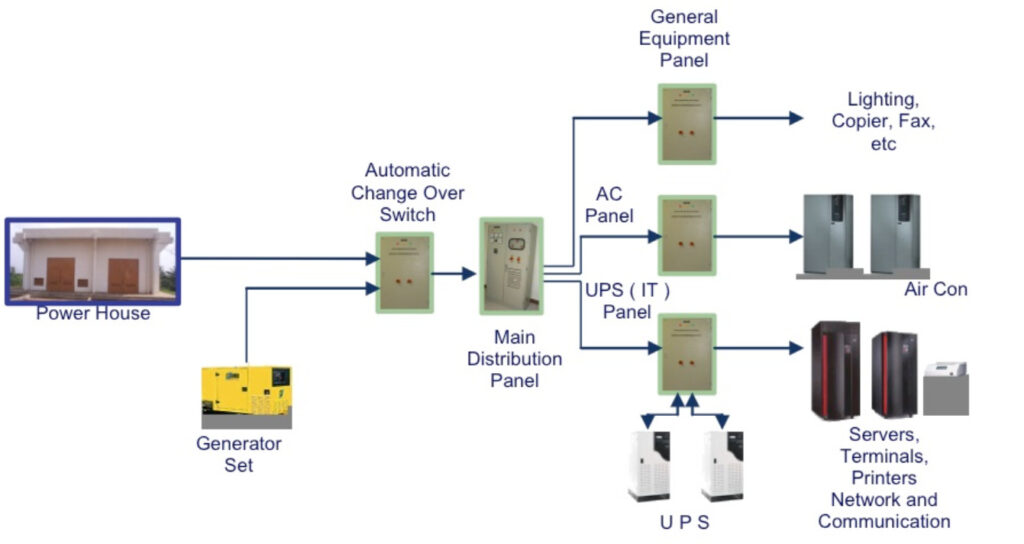
Disaster recovery planning ensures that organizations can restore systems quickly following cyberattacks, hardware failures, or natural disasters. IT support teams establish Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) to define acceptable downtime and data loss thresholds.
Cloud-based solutions from providers such as Amazon Web Services and Microsoft Azure offer redundancy and failover systems. However, these technologies require proper configuration and continuous monitoring by skilled IT support professionals.
Regular backup testing, penetration testing, and vulnerability assessments further reduce risk exposure. Without structured IT support, organizations risk prolonged downtime and irreversible data loss.
Building Digital Trust Through Reliability
Trust is earned through consistency and security. Customers expect uninterrupted service, secure transactions, and protection of their personal information. IT support teams ensure high system uptime through infrastructure monitoring and performance optimization.
Load balancing, redundant servers, and cloud failover systems reduce the risk of outages. By maintaining stable digital environments, IT support safeguards business reputation and customer loyalty.
Furthermore, compliance with industry regulations enhances trust. Whether addressing GDPR requirements in Europe or data protection laws elsewhere, IT support ensures adherence to legal standards, minimizing exposure to fines and legal complications.
Reliable IT support transforms technology from a potential vulnerability into a competitive advantage.
IT Support in Remote and Hybrid Work Environments
Remote work has expanded organizational flexibility but introduced new security challenges. Employees now access corporate systems from various devices and networks, increasing exposure to potential breaches.

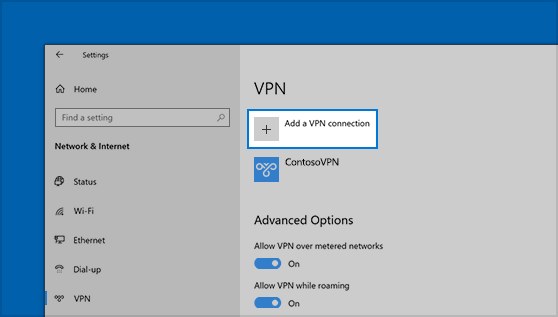
IT support teams implement Virtual Private Networks (VPNs), endpoint encryption, and remote device management tools to secure offsite access. Multi-factor authentication and strict identity verification prevent unauthorized entry.
Cloud collaboration tools must also be properly configured to ensure data privacy. By securing remote infrastructure, IT support enables productivity without compromising safety.
Managed IT Support vs. Internal Teams
Organizations often choose between maintaining in-house IT support teams or outsourcing to managed service providers. Each approach has distinct benefits.
Internal teams offer direct control and familiarity with company systems. Managed service providers, however, provide scalable expertise and 24/7 monitoring capabilities. Technology leaders such as IBM and Cisco Systems deliver enterprise-level solutions that smaller organizations may struggle to develop independently.
A hybrid model often proves most effective, combining strategic internal oversight with outsourced cybersecurity and monitoring expertise.
Conclusion: IT Support as a Strategic Safeguard
IT support is far more than a technical function—it is a strategic shield protecting organizations from digital threats. By ensuring cybersecurity, supporting compliance, managing risks, and enabling business continuity, IT support builds trust and operational resilience.
In a world where digital disruption can occur at any moment, proactive IT support strategies safeguard long-term sustainability. Businesses that invest in robust IT infrastructure and skilled support teams position themselves for growth, security, and trust in an increasingly complex technological landscape.